Last Updated on May 6, 2026
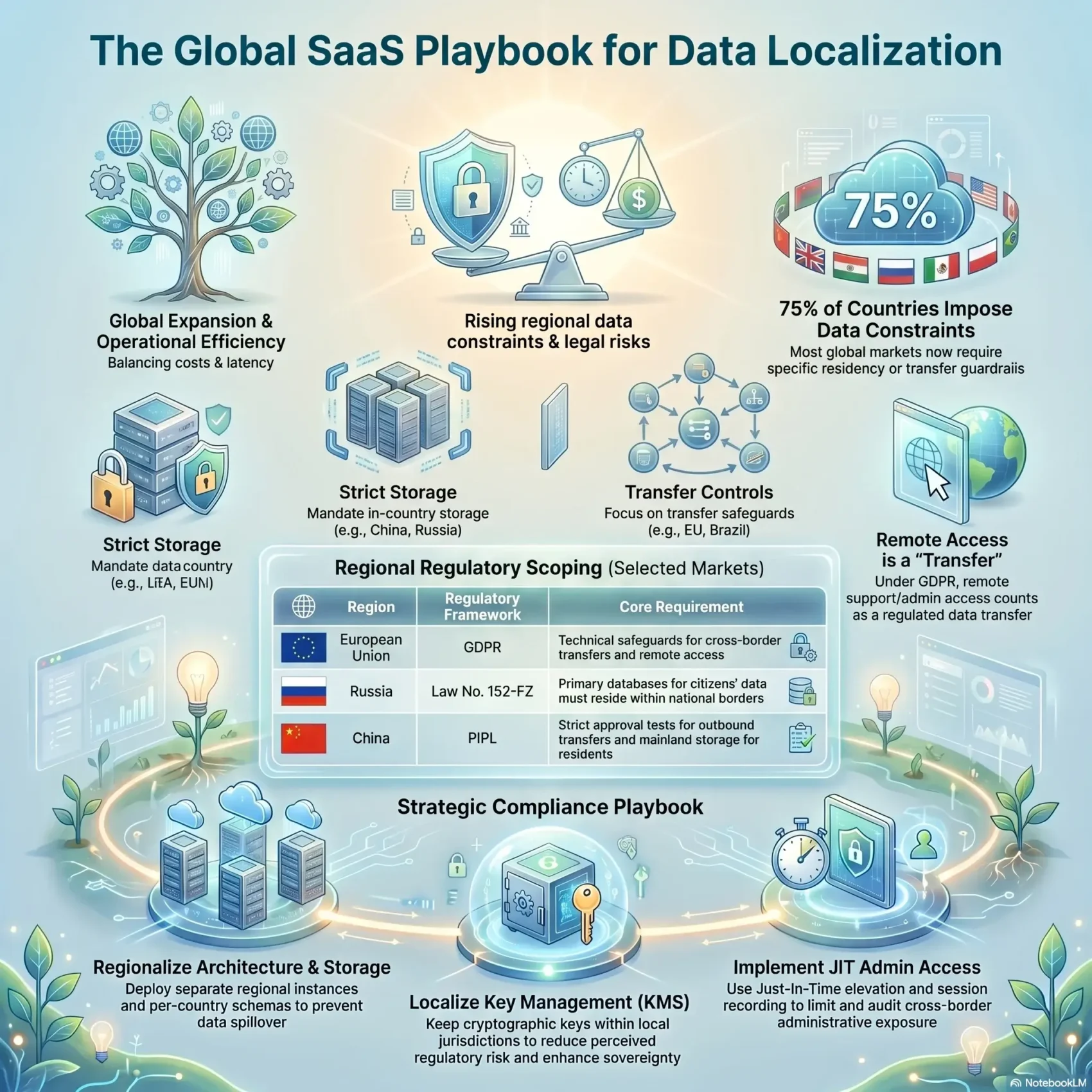
Your global expansion now starts with where you host and who can access information. Cloud tools and analytics make your products richer, but rising residency rules from the EU, Russia (152-FZ), UAE (DIFC/ADGM), Vietnam, and Saudi Arabia (CCF) change how you build and operate.
You’ll face choices about in-country storage, transfer controls, and team access. Some countries block cross-border flows outright. Others, like the EU, treat remote access as a transfer under GDPR. That affects support, logging, and engineering workflows even if storage stays inside a region.
Expect trade-offs among latency, resilience, and cost as you regionalize. Compliance and privacy requirements shape product design, GTM plans, and your operating model. This article gives a practical map to help you align architecture with regulatory reality and protect customers while you scale.
Key Takeaways
- New residency rules affect where you host and who can access records.
- EU GDPR, Russia 152-FZ, UAE free zones, Vietnam, and Saudi CCF each demand different remedies.
- Remote access can be a regulated transfer — plan support and logging accordingly.
- Regional storage raises trade-offs: latency, resilience, and cost.
- Build an inventory, scope jurisdictions, and document transfer controls for audits.
Why data localization laws matter now for your global SaaS strategy
When countries demand residency for sensitive records, your expansion timeline and costs change fast. Compliance is no longer a back-office checkbox; it must guide product, sales, and operations from day one.
Sectors such as health, finance, telecom, and payments are most affected. Those industries commonly face strict transfer requirements and extra certifications. Failing to adapt can trigger audits or service restrictions that block market access.
Plan strategically so you don’t overpay or miss revenue. Align sales promises with realistic delivery dates and build legal review into your roadmap. Choose vendors and region partners based on local certifications, lawful transfer mechanisms, and deployment speed.
- Architecture impact: separate regional instances and controlled admin access reduce enforcement risk.
- Operational impact: hire for regional support and map hosting availability before signing deals.
- Market impact: clear customer communications about privacy and protection can win trust in regulated countries.
What data localization means today: definitions, scope, and real-world implications
Clear definitions upfront save you time and costly rework when countries claim control over where information sits. Start with terms so legal, engineering, and security teams use the same vocabulary.
Different concepts, different obligations
Data localization is a legal mandate to keep records inside borders. Residency is your choice about where you host systems. Data sovereignty means the host country’s rules govern the records.
Who and what is covered
Personal data spans names, contact info, health, payments, and employment details. A data subject is the identifiable person whose rights attach when you process those records.
- Regulated categories often include payments, health, and telecom metadata.
- Logs, backups, and telemetry can carry personal information and fall under protection requirements.
- Control over who can access records—remote staff or vendors—matters as much as storage location.
“Where a record lives often dictates who can ask for it and how you must respond.”
Align your taxonomy across teams, map sensitive categories, and document transfer and access controls to meet privacy and data protection expectations during audits and RFPs.
Core drivers behind localization requirements: privacy, security, and enforcement
Many countries adopt in-country hosting to strengthen oversight, speed incident response, and grow local cloud markets. This mix of goals shapes what you must build and how you operate.
Governments often cite national security to justify residency. Faster incident response and lawful access for authorities matter most where finance, telecom, and health systems are at stake.
Those sectors face stricter in-country storage to reduce systemic risk and improve oversight.
Economic policy and market access
Many rules also serve economic aims. Requiring local hosting can spur jobs and investment in cloud centers.
For your business, that can mean higher costs but smoother market entry if you comply.
Digital protectionism versus genuine protection
Critics call some measures protectionism that blocks innovation and cross-border trade. Supporters argue the moves enhance privacy and protection for citizens.
- Link privacy goals to security mandates so your architecture meets enforcement expectations.
- Weigh market-access tradeoffs: comply and localize or choose not to enter certain countries.
- Use strong encryption and key locality to reduce the need for full repatriation of records.
“You’ll need to design for resilience, assuming enforcement can shift quickly and require rapid re-architecture.”
Plan messaging that explains how privacy and security benefits justify performance and cost impacts. That transparency helps customers and regulators trust your approach.
Benefits and trade-offs: compliance wins, operational costs, and performance
Balancing regulatory wins with engineering costs is a practical step in your expansion playbook. Regional hosting often improves latency for local users and makes your legal posture clearer. That can unlock market access and boost customer trust.
But expect higher infrastructure spend and more complex operations. Fragmented stores can limit cross-region analytics and raise total cost of ownership for logging, backups, and disaster recovery.
Staffing matters. You’ll likely hire regional SREs, security admins, and support to reduce cross-border access and to maintain audit trails.
- Quantify gains: market reach, better privacy signals, and a clearer compliance stance versus added cloud and ops overhead.
- Technical trade-offs: faster customer experience versus fragmented analytics and slower feature velocity.
- Risk mitigation: strong key management locality and encryption let some services stay centralized while lowering perceived risk.
“Pilot critical regions first, document controls for customers, and evaluate sovereign cloud or residency-as-a-service to speed compliant presence.”
How data protection regulation shapes localization: GDPR, CCPA, and beyond
Privacy-focused statutes reshape how you store, process, and let teams reach customer records across borders. These regimes set rules that affect where information sits, who can touch it, and how you prove protection to auditors and customers.
General principles that affect storage, processing, and access
Purpose limitation, minimization, security, and accountability are not legal buzzwords — they guide architecture.
You’ll map those principles into storage tiers, retention rules, and strict admin roles. That lowers risk and speeds audits.
Cross-border transfer mechanisms and adequacy concepts
GDPR governs processing in the EU and restricts transfers to countries without adequate protection. Importantly, remote access from abroad can count as a transfer.
Mechanisms include adequacy decisions, standard contractual clauses, and technical safeguards like encryption and key locality. Use transfer impact assessments to show your protections are essentially equivalent when needed.
- Align incident response timing and breach notices with regional requirements.
- Map subject rights (access, deletion, portability) to your multi-region systems.
- Include vendor due diligence that lists sub-processor locations and auditability.
“Plan for shifting rulings that may force quick contractual and technical pivots.”
EU and GDPR stance on localization and international transfers
How your teams access records often matters as much as the server’s physical address. Under gdpr, storage in the EEA, processing in-region, or remote access from outside can all qualify as a transfer. That means your architecture must assume transfers unless you can show safeguards.
When storage, processing, or access becomes a “transfer”
Transfers can be triggered by remote admin sessions, offshored support, cross-region telemetry, or CI/CD pipelines that touch EU-held personal data. Even logs and crash dumps count if they include identifiers.
Implications for multi-region SaaS architectures
Many teams run separate EU and non-EU instances to reduce transfer risk and simplify compliance. Logical segregation, region-aware controls, and just-in-time access help you limit unnecessary exposure.
- Segregation: prefer physical or strong tenant separation for EU users.
- Access controls: bastions, JIT, and detailed logging demonstrate proportionality.
- Key management: keep keys and separation of duties inside the EEA when possible.
“Document flows that show EEA records stored and processed in-region with audited exceptions.”
Russia: localization-by-default for personal data and its extraterritorial reach
If you serve Russian users, you must design flows so personal records originate in Russia before any overseas processing.
Russian Law No. 152-FZ mandates collection, recording, systematization, accumulation, storage, clarification, and extraction of Russians’ personal data in databases located in Russia.
Subsequent processing, transfer, depersonalization, and deletion may occur abroad only when the Russian master database stays in-country and is kept up to date.
How this affects your stack and ops:
- Design collection flows that route web forms, SDKs, and telemetry into Russian-hosted systems first.
- Segregate payment records so domestic transactions follow the National Payment System and remain stored in Russia.
- Restrict cross-border support and admin access; log exceptions and use just-in-time elevation when necessary.
You’ll also map triggers that make you an operator under the law — .ru domains, ruble billing, or Russian-language sites are common indicators.
“Prepare for Roskomnadzor audits with proofs of locality, vendor contracts, and clear master-replica update logic.”
Finally, update vendor agreements to require sub-processors to keep covered records in Russia and add remediation runbooks for takedown or service restriction risks.
China and strict localization models for personal information protection
PIPL and related frameworks require you to treat Chinese personal data with special care. Personal information about Chinese residents often must be stored and processed in mainland China, and outbound transfers face strict approval tests.
Scope which user sets must remain in-country and plan your hosting and key management accordingly. Keep cryptographic keys and KMS in local regions when required to reduce regulatory risk.
Inventory telemetry, logs, and support artifacts so you don’t leak identifiers across borders. Set independent CI/CD and monitoring for the China deployment to stop foreign access that could count as an unlawful transfer.
- Design approval workflows and security assessments for any outbound transfer.
- Restrict remote employee access with role-based controls and just-in-time elevation.
- Update privacy notices and consent flows to match PIPL transparency and purpose limits.
“Plan costs and timelines early — building a compliant presence in China affects product, ops, and vendor choices.”
Vietnam’s evolving framework: cybersecurity-led localization obligations
Vietnam’s regulatory mix forces you to treat privacy and network security as a single operational priority. Multiple statutes — the Cybersecurity Law (2018), cyberinformation rules, sector regulations, and labor code clauses — together shape what your business must do.
You must capture consent before collecting, sharing, or transmitting personal data and define protection duties in third‑party contracts. Publish clear privacy notices and honor deletion requests promptly.
Store records securely to meet ISO/IEC‑compatible technical standards and log consent and processing for audits. Keep employee records separate when labor rules impose specific retention or access limits.
- Identify which statutes apply for each product and sector.
- Document processing, consent logs, and technical safeguards for inspections.
- Design incident response with local notification and evidence preservation.
- Audit vendors in‑country for protection alignment and cross‑border transfer risks.
“Monitor draft decrees and guidance closely — enforcement can tighten requirements or clarify in‑country storage triggers.”
UAE and free zones: sector rules and finance/telecom data restrictions
UAE oversight is fragmented: free zones like ADGM and DIFC run their own regimes while federal and sector regulators set separate expectations on the mainland.
In practice, that means you must map where customer records reside and which regulator governs them. ADGM’s Office of Data Protection and the DIFC Commissioner handle free zone compliance and inquiries.
ADGM, DIFC, and sector-specific protection regulation
Payments and telecoms face the tightest controls. The Central Bank’s Digital Payment Regulation forces payment service providers to keep all user and transaction records stored inside the UAE.
- Payments: design architectures and backups so UAE-stored transaction information never leaves the country.
- Telecom: collect explicit subscriber consent before sharing records and add contractual confidentiality with third parties to match TRA expectations.
- Health & government: apply DHCC health safeguards and follow the Dubai Data Law for government exchanges.
Practical steps: segregate free zone operations from mainland systems, validate vendor locations, and align retention and breach plans to both free zone regulations and sectoral requirements.
“Coordinate early with ADGM or DIFC regulators to clarify obligations and notify incidents when required.”
Saudi Arabia’s Cloud Computing Regulatory Framework and data protection expectations
Saudi Arabia’s cloud framework demands clear role definitions between providers and customers before you deploy.
The CITC Cloud Computing Framework sets registration, classification, and breach-notification requirements you must meet.
Classify your content under the KSA categories and align controls to each category’s sensitivity. Implement breach workflows that match the regulator’s timelines and reporting steps.
Register as required and keep documentation that shows who is the CSP and who is the customer for audits and vendor checks.
- Limit cross-border admin access with granular logging and just-in-time elevation for audits.
- Evaluate local or sovereign cloud regions for sector-specific residency preferences.
- Review contracts for sub-processor transparency, audit rights, and in-country key custody options.
Design DR and backup plans that respect KSA classification and avoid unapproved copies abroad. Train teams on terminology, regulator expectations, and the compliance evidence you’ll present to customers.
“Build customer assurances around privacy and security that mirror KSA best practices.”
India, Brazil, and other key markets: differing paths to compliance
India and Brazil take distinct approaches that change how you build regional controls and user-facing notices. India leans on sector rules and notifications, while Brazil’s LGPD mirrors gdpr principles without a blanket requirement to keep records inside borders.
India’s sectoral and notification-based approach
In India, policy is still evolving. Financial records often must remain on local servers, and the government can restrict flows to specific countries by notification.
You should plan storage and partner selection around banking and payments triggers. Track official notices closely so your cross-border transfers meet new requirements quickly.
Brazil’s LGPD and international transfer safeguards
Brazil’s LGPD borrows from gdpr. It emphasizes lawful bases, consent, and robust rights for the data subject.
You’ll build playbooks that document lawful basis choices, strengthen consent UX, and apply contractual or technical safeguards for transfers.
- Support subject rights with standard SLAs and mapping tools.
- Perform transfer due diligence for Argentina, Colombia, Peru, and Uruguay and use adequacy or consent paths where available.
- Anticipate South Korea’s strict outbound approvals and minimize unnecessary cross-border movement.
“Document country-specific deviations from your global baseline so auditors see a coherent control set.”
Practice tip: harmonize privacy notices, update contracts for cross-border clauses, and choose regional partners with sector experience. Monitor legislative shifts in India and Brazil so your compliance posture stays ahead of new requirements.
Operational playbook: how you can comply with localization requirements
Start by mapping how customer records move inside and between the countries you serve. That inventory becomes the foundation for scoping, technical controls, and your privacy playbook.
Data mapping, classification, and jurisdictional scoping
Conduct a full map to pinpoint what personal and regulated information you hold, where it flows, and which jurisdictions touch it. Classify items by sensitivity and regulatory scope—payments, health, and telecom metadata deserve special flags.
Then define routing rules that send each category to the correct region and block unlawful paths. Use tags in storage and processing platforms so engineers and auditors can see scope at a glance.
Consent, contracts, and third-party transfer controls
Systematize consent capture, withdrawal, and proof. Align notices with local transparency requirements and log consent events for audit trails.
Harden contracts with SCCs, local addenda, and clear sub-processor obligations. Implement transfer approval workflows that record legal bases and extra technical safeguards.
Documentation, audits, and continuous monitoring
Maintain ROPAs, DPIAs/TIAs, incident logs, and evidence of technical and organizational protection measures. Non-compliance can bring fines, bans, or lost market access, so keep records ready.
- Continuous monitoring for movement, access anomalies, and vendor posture changes.
- Privacy-by-design in tickets, code reviews, and deployment gates.
- A compliance committee across legal, security, product, and ops to steer decisions.
Practical support: consider residency-as-a-service providers to meet country-specific storage and processing obligations quickly. For templates and governance pointers, see our governance playbook.
“Strong governance and continuous monitoring are the cheapest insurance against enforcement risk.”
Architecting for compliance: storage, processing, and access by country
Treat each jurisdiction as an operational boundary. Map which user sets must remain in-region, then build isolation to match rules and business needs.
Regionalized stores and segregated environments
Design regionalized layers with strict tenancy boundaries. Use per-country schemas, queues, and storage accounts so regulated workloads do not spill into other regions.
Keep keys and crypto material local by leveraging regional KMS and HSMs. That reduces cross-border risk and meets many compliance requirements.
Logs, support access, and developer workflows
Treat logs, metrics, and traces as regulated content. Redact or tokenize identifiers before any cross-border aggregation.
- Adopt break-glass, JIT admin access with session recording tied to incident tickets.
- Separate build pipelines per region to avoid artifacts that embed personal details leaving a jurisdiction.
- Enforce least privilege for developers; use masked sets or synthetic test records.
- Verify backups and DR replicas stay in-region, with geo-redundancy only to lawful jurisdictions.
“Regional separation and policy-as-code make residency obligations auditable and repeatable.”
Centralize policy as code to enforce residency at both infrastructure and application layers. Finally, offer local support channels to avoid cross-border screen sharing and protect user privacy and security.
Security-by-design under localization: encryption, access control, and telemetry
Put cryptographic separation and tight access rules at the center of your regional builds. This reduces transfer risk and makes audits simpler.
End-to-end encryption and key management locality
Implement end-to-end encryption for transit and rest, and use per-region keys to preserve locality. Keep key custodianship separate by jurisdiction and rely on hardware-backed stores for highly sensitive workloads.
Zero trust access, MFA, and regulated monitoring
Zero trust stops implicit trust. Enforce strong MFA, device posture checks, and continuous verification for all privileged access.
- Instrument telemetry that flags cross-border transfers and odd admin actions in real time.
- Tokenize or pseudonymize personal identifiers where possible to reduce exposure.
- Apply DLP and CASB rules tuned to regional boundaries and export controls.
Automate audit trails so you can show who accessed what, when, and how. Define logging policies that keep forensic value without exporting regulated content and run incident drills for key revocation and regional isolation.
“Strong encryption, local key custody, and continuous monitoring are the best proof you can give auditors and customers.”
For architecture patterns on regional edge and residency, see our regional edge and residency patterns.
Enforcement and penalties: what non-compliance can cost your business
Failing to meet cross-border obligations can trigger fines, service restrictions, and lengthy remediation costs. Regulators worldwide are more active, and enforcement now includes both financial and operational penalties. You need to see risk as a business cost, not just a legal item.
Consequences range from administrative fines to blocked services and litigation. In some countries, authorities can ban apps, restrict network traffic, or remove your product from local app stores. Russia and several other jurisdictions have shown they will limit service access when rules are breached.
Fines, service bans, and reputational damage
Quantify financial exposure: regulatory fines, legal fees, and the cost to fix systems can add up quickly. Build realistic scenarios and insurance reserves so you are not caught off guard.
- Monetary risk: administrative penalties and remediation costs, plus potential private litigation.
- Market access: service blocking, app store removal, or forced suspension in specific countries.
- Reputation: lost trust, customer churn, and partner terminations after a privacy incident.
Track enforcement patterns and regulator priorities so you can predict scrutiny. Strengthen evidence readiness: logs, contracts, and audit trails reduce penalties and speed resolution.
Plan crisis communications for regulators, customers, and the press. You should also prepare corrective action plans with clear milestones and consider exit options where compliance is not viable. Integrate lessons into continuous monitoring and control improvements to lower future risk.
“Showing prompt remediation and transparent proof of compliance often softens penalties and restores customer confidence.”
data localization laws: a closer look at global trends and what comes next
Most markets now expect some form of residency or transfer guardrails for sensitive systems. Around 75% of countries impose constraints, from light export controls to strict in-country storage.
Compare models: strict storage mandates in China and Russia contrast with transfer-focused regimes in the EU and Brazil. Sector rules—financial and telecom in the UAE, for example—add another layer of complexity.
Watch India as it pilots notification and sectoral triggers that may become a blueprint for other large markets.
- Geopolitics will shift adequacy and permitted pathways.
- Vendors will expand location controls, local certifications, and in-country key custody options.
- Your team should build harmonized standards that flex to stricter overlays without fragmenting services.
“Invest in regulatory intelligence and modular designs so you can roll compliant patterns into new countries quickly.”
Plan a 12–24 month roadmap that funds audits, sovereignty-driven cloud options, and membership in industry groups shaping best practices. That keeps you ready for changing regulations and privacy protection requirements without emergency rewrites.
Conclusion
End with a pragmatic playbook that turns requirements into repeatable engineering and operational steps.
Start by mapping what you hold, then segregate regions, lock down access, and document every control. Use regional architecture, encryption with local key custody, and just-in-time admin elevation to meet compliance and protect customers.
Operationalize consent, contracts, and transfer safeguards so movement is lawful and auditable. Standardize monitoring and evidence collection so regulator requests become routine, not crises. Balance privacy and protection gains against cost with an architecture-first mindset.
Choose vendors who support location controls, sector certifications, and clear sub-processing. Iterate as countries update requirements and treat localization as an ongoing capability in how you build and run your global services.