Last Updated on February 23, 2026
You need a clear, practical roadmap to protect customer data and run your business with confidence.
Countless security and data standards exist, and choosing the right one can feel overwhelming. A good framework turns scattered rules into a single, repeatable approach that reduces risk and speeds audits.
With the right strategy, you can align information controls across HIPAA, PCI DSS, and other standards to cut duplicate work and lower costs. We’ll show how to connect data protection and incident response so you can act faster when threats appear.
Along the way, you’ll learn who to involve, which controls to pick, and how to measure progress without overwhelming teams. For practical tools, try our privacy policy generator as a starting point for clear consumer-facing language.
Key Takeaways
- A unified approach simplifies audits and saves time.
- Mapping data types helps you pick the right controls.
- Common controls let you scale security across regulations.
- Linking incident response to policies reduces breach impact.
- Small, measured steps win—scope, train, monitor, improve.
What You’ll Learn in This Ultimate Guide
In this guide, we break down how to choose and adapt standards so your teams spend less time duplicating tasks and more time protecting data.
Adopting a consistent approach streamlines compliance, cuts duplicated effort, and aligns controls with enterprise objectives. You’ll see when to use common standards like NIST CSF or ISO 27001 and how those choices map to rules such as GDPR, CCPA, and HIPAA.
You’ll get a clear, step-by-step roadmap for scoping, control selection, training, and continuous monitoring. The guide shows how to tailor controls to your operations and document justified exceptions so audits are simpler and faster.
- You’ll learn the difference between privacy and security and why both matter to program effectiveness.
- You’ll learn how to align regulations to frameworks to avoid duplicative work and conflicting controls.
- You’ll get metrics to measure success—DSAR SLAs, incident response times, and audit outcomes.
Finally, you’ll receive practical advice for building a cross‑functional team of legal, security, IT, and business owners. This helps turn requirements into action and reduces risk to your customers and organization.
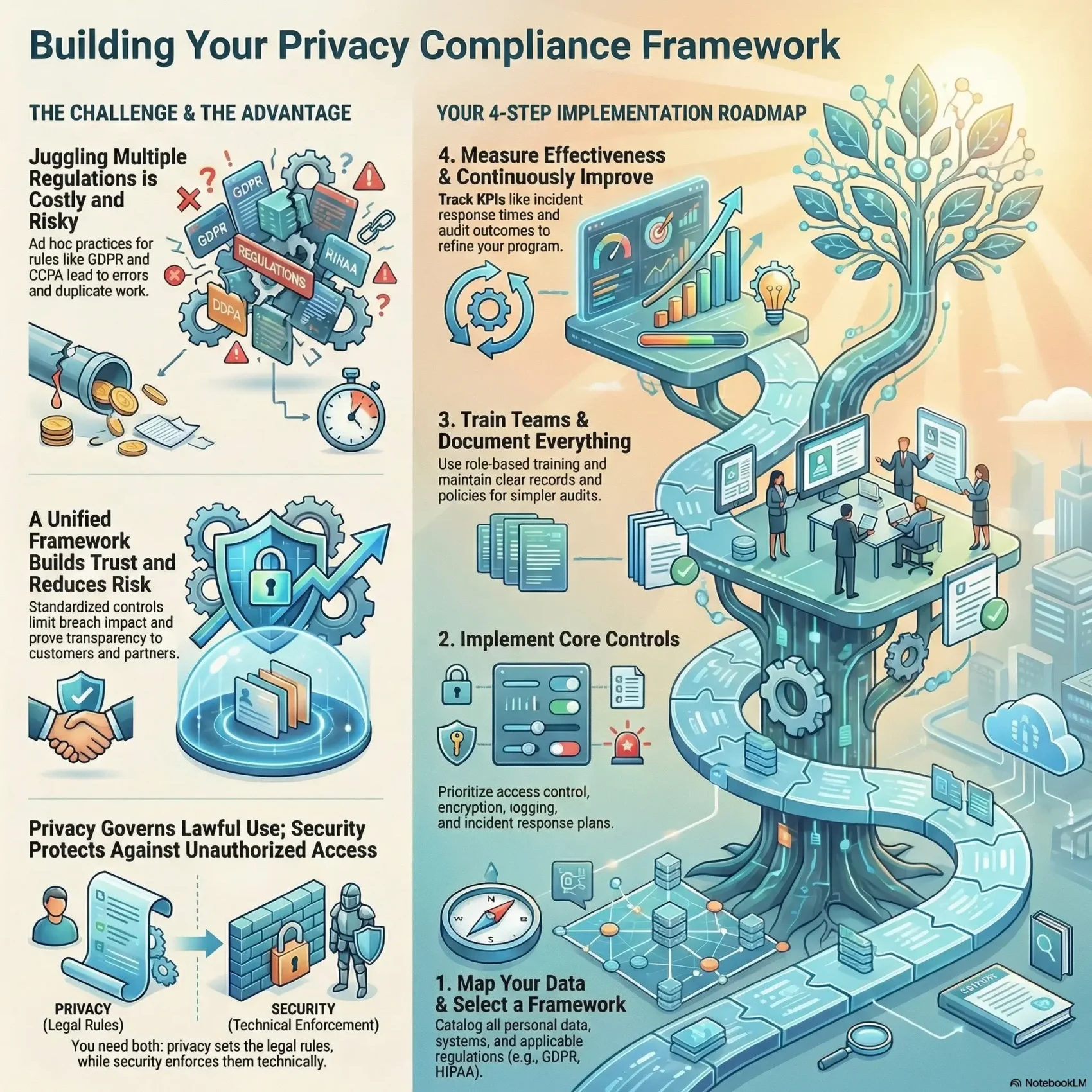
Understanding the privacy compliance framework
Start with a structured set of processes that help you find, manage, and reduce risk across systems and teams.
What a privacy framework is and why it matters now
A privacy framework is the structured set of processes you use to identify, manage, and reduce risk across your organization. It collects policies, controls, and routines so your teams act consistently when handling personal information.
Modern firms juggle multiple regulations and standards. That complexity makes ad hoc practices costly and error prone.
Core principles: structure, universality, and adaptability
Core principles like clear structure, universal controls, and flexible design let you scale protections from small projects to enterprise programs.
“Good governance turns rules into repeatable action — speeding responses and trimming duplicate work.”
- Define processes for data mapping, consent, and third‑party oversight.
- Use proven standards such as FIPPs, NIST Privacy Framework, and ISO to mature practices.
- Measure results: faster consumer responses, clearer controls, and consistent governance.
Adopting a single program gives you a practical backbone for policies, training, and continuous improvement.
Data privacy vs. data security: the difference that shapes your strategy
How you treat personal data legally differs from how you defend it against cyber threats. You need both sides to build trust and reduce risk. One sets rules for collection, use, sharing, and retention. The other stops unauthorized access and breaches.
Privacy governs lawful use; security protects against unauthorized access
Privacy defines the legal requirements and the rights of individuals under laws like GDPR, CCPA, and HIPAA. It tells you what you may collect and why.
Security puts those policies into action. Technical and administrative measures — encryption, access control, logging, and incident response — protect information across your systems.
- Separate policy decisions (lawful use) from technical practices (defense) so nothing falls through the cracks.
- Map legal requirements to concrete controls: tie a data retention rule to automated deletion and access restrictions.
- Don’t assume strong security equals legal compliance; align controls to protect individuals’ rights and reduce exposure.
- Design workflows that embed consent, purpose limitation, and role-based access to make audits and reporting simpler.
“Treat policy and technical controls as partners: one sets the rules, the other enforces them.”
Why frameworks build trust: business value, risk reduction, and competitive edge
A structured program can turn data protection into a measurable business advantage. You get fewer surprises, faster responses, and clearer reporting that executives and customers value.
Protecting personal information and reducing breach impact
Standardized controls limit exposure and shorten recovery time when incidents happen.
You’ll reduce human error, cut breach costs, and keep customers from walking away.
Ensuring compliance with regulations and demonstrating transparency
Consistent notices, records, and measurable performance help you show compliance and build trust.
That transparency speeds sales cycles and reassures partners during audits of GDPR, HIPAA, or PCI DSS.
Standardizing practices for measurable, continuous improvement
When teams follow the same procedures you lower mistakes, simplify training, and scale faster.
- Connect adoption to business outcomes like reduced breach costs and faster deals.
- Use continuous monitoring and regular assessments to keep pace with threats.
- Align risk management to priorities so you invest where it delivers real protection and value.
“A repeatable program makes security and information management an auditable advantage.”
User rights you must operationalize (GDPR, CCPA/CPRA) to sustain trust
Handling consumer requests at scale means turning legal entitlements into clear, testable workflows. You must map rights, build repeatable steps, and prove you meet deadlines.
Access, deletion, and opt-out rights at scale
GDPR grants individuals access, rectification, and erasure, and demands prompt breach reporting with fines up to €20M or 4% of global revenue.
CCPA/CPRA gives rights to know, delete, and opt out, plus non‑discrimination protections and penalties up to $7,500 per intentional violation.
Designing processes for timely breach notification and consumer requests
You’ll translate these rights into intake, verification, fulfillment, and recordkeeping that run across your systems.
- Design DSAR pipelines to meet response windows and reduce operational disruption.
- Automate deletion and opt‑out across data stores and vendors to stop re‑collection.
- Create breach playbooks with roles, timelines, and stakeholder messages to limit fines.
- Centralize request tracking to measure SLAs and prove compliance in audits.
“Operational rules that are simple to follow become your best defense against fines and lost trust.”
The global landscape: key privacy and security frameworks you can leverage
A clear inventory of international and sector rules lets you match controls to real operational needs. Start by mapping the major standards that affect your systems, people, and vendors. That map helps you choose the right controls and cut duplicate work across teams.
Privacy-focused standards and regulations
Top sets to consider:
- GDPR — the strict EU rule for personal data across the European Union.
- CCPA/CPRA — strong consumer rights in California that influence U.S. practice.
- NIST Privacy Framework, ISO 27701, ISO 29100, PDPA (Singapore).
Security-focused allies
Complementary tools you can align with:
- NIST CSF and ISO 27001/27002 for information risk programs.
- CIS Controls, PCI DSS, COBIT, HITRUST, FISMA, FedRAMP, IRAP for sector needs.
- Use CIS Controls for practical security steps that support your data goals.
“Many privacy standards pair well with long‑standing cybersecurity counterparts, easing integration across the enterprise.”
What you’ll gain: a snapshot of the most relevant frameworks and when each is used, guidance on mapping your operations to the right set, and a way to evaluate maturity so your organization invests where it matters most.
How to choose the right framework for your organization
Focus on what you actually run day to day. Start by mapping the types of data you collect, the geographies you touch, and the industry rules that matter. That reality check keeps selections practical and implementable.
Match industry, data types, and geographic scope to requirements
Inventory your lines of business and the information each handles. Note whether you process EU or California resident data, health records, or payment card details.
Use that list to find mandatory standards—HIPAA for health, PCI DSS for retail, GDPR or CCPA by location—and mark must-have compliance requirements.
Assess risk profile, maturity, and business objectives
Score your organization’s risk and management maturity. A small startup may pick SOC 2 or ISO 27001 for cloud trust, while federal work points to NIST or FedRAMP.
Choose an approach that matches your systems, vendor ecosystem, and strategic goals—customer trust, speed to market, or audit readiness.
- Document your rationale so leadership can sign off quickly.
- Avoid sprawl: pick standards you can map together with common controls.
- Prioritize based on business impact and implementability.
Who should be involved: building your cross‑functional selection team
Assembling the right team ensures data decisions reflect how information really flows across your company. You want people who know the rules, systems, and daily touchpoints where data moves.
Privacy, legal, compliance, and risk management
Include counsel and privacy experts to interpret obligations and reduce regulatory risk. Add compliance and risk management to score choices against legal exposure.
Keep internal audit advisory and independent so it can later test controls without conflict.
Cybersecurity, information security, IT leadership, and key business owners
Bring cybersecurity and information security to map technical controls to program goals.
Include CIO/CTO and IT for integrations, plus business owners in marketing and HR who handle customer and employee data.
Accountability: who makes the final decision
- Assemble cross‑functional stakeholders so you cover data flows end to end.
- Document roles for testing, operations, and ongoing management.
- Designate one accountable leader — often the CPO or a senior risk leader — to make final calls and keep momentum.
“Clear roles and a single decision owner stop analysis paralysis and speed practical work.”
With this team, your organization will align security and business goals and choose a framework that fits your operations.
Mapping regulations to frameworks: streamline compliance and avoid duplication
Create a single control matrix that shows which measures satisfy multiple rules and where you still need extra steps. This makes it easier for you to reduce duplicated work and show clear evidence during audits.
Start small by listing the data flows, the technical controls you already use, and the legal requirements that apply to those flows. Map each requirement to one or more controls so you can see overlap at a glance.
- You’ll build a control matrix aligning gdpr, CCPA/CPRA, and HIPAA to ISO 27701, the NIST Privacy Framework, and ISO 27001.
- You’ll identify overlaps that let a single control satisfy multiple obligations and cut audit fatigue.
- You’ll find gaps where extra processes or tools are required to meet specific requirements.
- You’ll leverage NIST PF alignment with NIST CSF and SP 800-53 to speed technical integration.
- You’ll use ISO 27701 to extend your ISO 27001/27002 ISMS with privacy-specific additions.
Document mappings and justified exceptions so your team can maintain the matrix, measure effectiveness, and decide where to adopt gdpr principles globally—even outside the european union.
“A compact control map turns complex rules into repeatable action and makes audits far less painful.”
Implementation roadmap: from scoping to continuous monitoring
Start with a practical plan that turns policy into repeatable tasks across teams and systems.
Scope personal information, systems, processes, and third parties
Begin by cataloging all data and where it lives. Map personal data, the systems that store it, business processes that use it, and every third party with access.
That map becomes the foundation for risk scoring and remediation planning.
Tailor controls to your operations and risk tolerance
Perform a gap assessment against the selected standard and prioritize fixes by risk and business impact.
Avoid copy/paste controls. Adapt technical and procedural controls so they match how your teams operate.
Communicate, train, and manage change across stakeholders
Plan frequent, focused communications for affected teams.
Use short trainings and role-based guides so staff know what changes mean day to day.
Measure effectiveness and iterate based on audits and metrics
Establish a cadence for testing, monitoring, and management reviews.
“Standardized procedures and continuous assessment let you evolve controls as threats change.”
- Define KPIs and audit checkpoints to prove effectiveness.
- Document exceptions and update them after each audit.
- Integrate change management to prevent control drift over time.
- Use metrics to drive remediation and repeat the cycle.
Controls that matter: from access management to audit logging
Start by locking down who can access data and how you log every significant action. That focus gives you fast wins and a clear path to stronger security across your systems.
Core control set: access control, encryption, logging, incident response, vendor risk
Build a compact control set that targets real risk. Prioritize access control to enforce least privilege and strong authentication across users and vendors.
- Encrypt sensitive data at rest and in transit to limit exposure when attacks reach a system.
- Centralize logging and monitoring to spot anomalies and speed investigations.
- Plan and rehearse incident response with clear roles, runbooks, and tabletop exercises to shorten recovery time.
- Assess vendor risk with standard due diligence, contract clauses, and ongoing checks.
Testing effectiveness with audits, assessments, and penetration testing
Validate your controls through audits, targeted assessments, and regular penetration tests. Use these tests to measure effectiveness and fix gaps quickly.
“CIS Controls, PCI DSS, and ISO 27001/27002 give you practical steps to protect data, ensure logging, and harden systems.”
Align your control set to recognized standards so your practices meet business requirements and scale across audits. Regular testing keeps your security posture honest and improves management over time.
Documentation and transparency: prove compliance and enable audits
Good documentation makes it simple to show what you do, why you do it, and who owns each step. Keep records tight, clear, and tied to technical evidence so reviews run smoothly.
Policies, records, and mapped information
Create a compact policy stack that turns high‑level rules into actionable procedures for daily teams.
Maintain data inventories, maps, and records of processing to show purpose, legal basis, and retention. Document control mappings and any tailoring you apply.
Exceptions, evidence, and roles
- Document exceptions with business and technical justifications and a defined risk treatment.
- Keep evidence repositories with training logs, test results, and control artifacts for fast audit response.
- Map controls to regulations and requirements so internal and external audits take less time.
“Transparency through clear records turns audits into routine checks rather than surprises.”
Assign owners and review cadences so your documentation stays current as systems and processes evolve. This approach helps stakeholders trust your data handling and supports stronger privacy and regulatory posture.
Framework spotlights: what to expect from leading standards and regulations
Leading standards each carve a different path for how you handle and protect personal data across borders.
GDPR and the European Union
GDPR applies extraterritorially and centers on lawful bases, consent, and strong data subject rights like access and erasure.
Fines can reach €20M or 4% of global revenue, so its requirements shape many global programs.
CCPA/CPRA
CCPA/CPRA gives consumers rights to know, delete, and opt out. Notices and non‑discrimination rules change how you design data flows.
Penalties include statutory damages and up to $7,500 per intentional violation.
HIPAA vs. HITRUST
HIPAA mandates safeguards for ePHI; HITRUST CSF bundles multiple standards and offers certification pathways to simplify audits.
ISO 27001 and ISO 27701
ISO 27001 defines an ISMS; ISO 27701 extends that to a PIMS and can be certified together to unify security and privacy controls.
NIST CSF and NIST Privacy Framework
Use NIST CSF’s five functions for risk management and the NIST Privacy Framework for aligned terminology and processes.
Other standards and use cases
- PCI DSS: cardholder data controls.
- COBIT: governance for IT and risk.
- FISMA / FedRAMP / IRAP / PDPA: federal or national scopes and cloud authorization.
“Map these rules to your control set so you meet requirements efficiently and reduce audit fatigue.”
Real‑world alignment: when multiple frameworks overlap
Overlapping obligations become manageable when you map common controls to each rule and run one testing cycle.
ISO 27002 is a practical starting point to speed work across HIPAA, SOX, PCI DSS, and GLBA. It gives you a proven control catalog you can map to regulation‑specific needs.
Using ISO 27002 to accelerate HIPAA, SOX, PCI DSS, and GLBA alignment
Start by mapping ISO 27002 controls to each law. Group matching controls so one control answers multiple obligations.
Where gaps remain, define compensating controls and document why they work. That makes your audit narrative stronger and easier to defend.
Designing a common control set that scales across audits
Create a single control set that your teams apply across systems and operations. Keep an evidence library that auditors can reuse during different assessments.
- Example: centralize access logs and retention proofs to satisfy several standards at once.
- Assign control ownership and a testing schedule that maps to your audit calendar.
- Measure time saved and risk reduced after consolidation to justify continued investment.
“A unified control set turns separate reviews into one repeatable process.”
Keep the catalog current as standards evolve so you avoid drift and control bloat. This approach reduces duplicate testing, lowers audit fatigue, and strengthens your security and data management practices.
Risk management in action: assessing, prioritizing, and remediating
Turn scattered risk signals into an organized program that drives targeted action. Use a repeatable risk management process to map threats, rank impact, and pick the right controls. Frameworks like NIST CSF and ISO 27001 guide assessment and continuous monitoring so you can focus work where it matters.
Threat modeling and data protection impact assessments
Threat modeling helps you spot likely attack paths and weak points in information flows and systems. Use DPIAs for high‑risk processing to test legal and privacy requirements and reduce exposure.
Tracking remediation for measurable effectiveness
Translate findings into clear remediation activities with owners, deadlines, and success criteria. Track closure and validate fixes with targeted tests and audits.
“A short, repeatable assessment then proves whether your fixes actually reduce risk.”
- Establish a repeatable assessment that informs control selection and prioritization.
- Run DPIAs for high‑risk data processing and document requirements.
- Track remediation to closure and validate effectiveness with tests.
- Report risk and business impact to leadership with clear metrics.
privacy compliance framework metrics: how you measure success
Track clear, business‑focused indicators so leaders see how your data program reduces risk and cost.
Good metrics make management decisions simple. They show both operational health and the program’s effect on customers and revenue.
Program maturity, DSAR SLAs, incident response times, and audit outcomes
Define a compact set of KPIs you can measure reliably. Start with DSAR intake‑to‑closure SLAs, accuracy, and customer satisfaction for request handling.
Measure incident detection and response times to validate readiness and containment. Shorter times mean fewer impacted records and lower remediation cost.
- Audit outcomes: track findings, issue aging, and reoccurrence rates to check control health.
- Assess maturity across governance, the data lifecycle, training, and third‑party oversight.
- Monitor training completion and policy attestation to reinforce accountability.
- Link metrics to business value—reduced costs, faster deals, and stronger customer trust.
Build dashboards that keep executives and teams aligned on priorities. Use visual KPIs to translate technical activities into business results and to guide next steps.
“Measure what matters: clear SLAs, incident timelines, and audit signals tell you if controls are working.”
For practical guidance on aligning program metrics with broader business goals, see our piece on ESG and SaaS business strategies. It shows how linking operational metrics to executive priorities speeds adoption and funding.
Conclusion
When your program ties controls to business goals, you turn obligations into measurable outcomes. You’ll choose and tailor a plan that fits your industry, systems, and data. This makes security and privacy work practical for teams and leaders.
Selecting, mapping, documenting, and communicating are the steps that make a chosen framework effective. Focus on the controls that matter, test them often, and keep management engaged. These practices reduce risk and simplify audits.
Track simple metrics, revisit scope and risk, and update controls as your business changes. Do this and you’ll protect information, prove requirements, and build lasting customer trust.