Last Updated on May 18, 2026
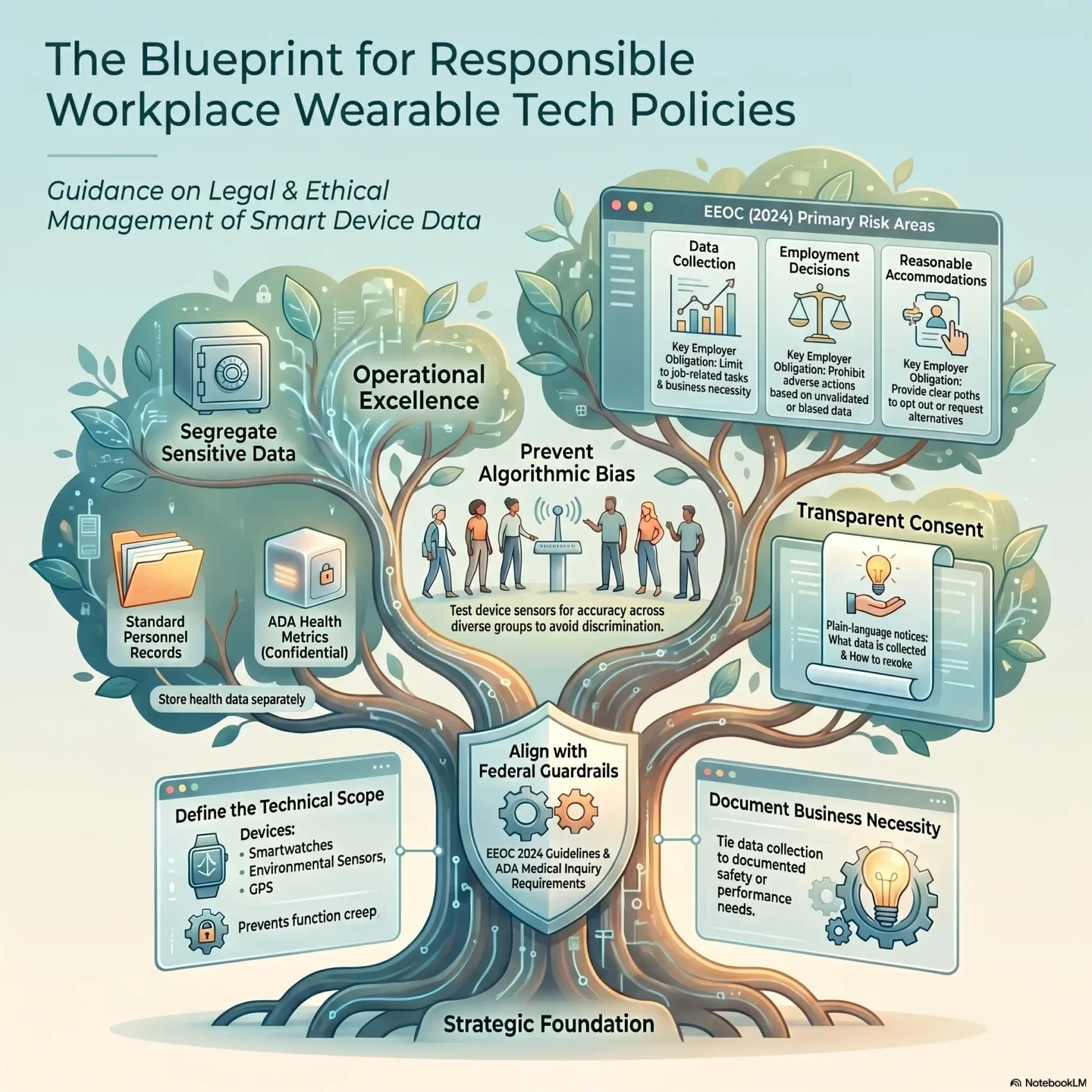
You need a clear plan to manage how devices collect information at work. On December 19, 2024, the U.S. Equal Employment Opportunity Commission flagged risks when employers gather health, productivity, or location data. Regulators such as the NLRB also warned about surveillance that can affect employee rights.
A good program protects people and your business. It defines what devices and data are covered, limits who can access information, and sets steps for reasonable accommodations. States including Illinois, Texas, and Colorado already restrict biometric uses, while Hawaii and New Jersey added notice rules for location tracking.
When you craft your approach, aim to reduce legal exposure and build trust. A short, practical document that explains collection, use, retention, and security helps managers and employees know what to expect. Adopt governance so this becomes part of daily operations, not a shelf document.
Key Takeaways
- Frame your policy as business-critical: it protects staff and guides data handling.
- Define scope clearly: health metrics, location, and device classes must be listed.
- Limit access and explain why information is needed to reduce legal risk.
- Align rules with federal and state guidance, and watch evolving requirements.
- Set manager expectations and embed governance so the program stays active.
Your Goal and Search Intent: Why You Need a Wearable Tech Policy Now
Start with a simple goal: protect workers while using device data responsibly. You must balance safety, productivity, and compliance so your program helps the business and respects employees.
The EEOC’s 2024 fact sheet highlights three risk areas: collecting information from devices, using information for employment decisions, and reasonable accommodations. The NLRB also warned that monitoring tools can affect Section 7 rights.
To reduce legal exposure and ease stakeholder concerns, map where data comes from, where it goes, and who can access information. That map should drive rules on collection, retention, and security.
Aligning policy with productivity, safety, and compliance
- Be explicit: list use cases that justify data collection and tie them to business needs.
- Limit access: guard health and location information to protect privacy and rights.
- Measure outcomes: fewer incidents, faster reviews, and clearer workflows.
Reducing risk while building employee trust
Address perceived surveillance by explaining choices and offering opt-outs where feasible. Clear communication shows commitment to rights and builds trust with employees and employers alike.
“Transparency and proportional controls turn concerns into manageable practices.”
What Counts as a Workplace Wearable and What Data Is Collected
Start by listing the devices you may deploy so you know what data you will collect and why.
Common examples include smartwatches, rings, environmental sensors, smart glasses and helmets, exoskeletons, and GPS units.
From smartwatches to sensors, glasses, helmets, and GPS devices
Map the full range of devices so you can clarify which are in scope for your program. This inventory helps you separate routine telemetry from sensitive readings.
- Devices to consider: smartwatches, rings, environmental monitors, smart glasses, helmets, exoskeletons, and GPS trackers.
- Personal gear: note when employees must share data from their own wearables and how that changes your obligations.
- Out-of-scope data: state whether off-duty activity or private health logs are excluded to limit concerns.
Biometric data, location tracking, and activity information explained
Be explicit about the data collected. Examples include heart rate, sleep, steps, exertion, fatigue indicators, hazard proximity, and location coordinates.
Distinguish types: operational telemetry (like steps or proximity alerts) can have different retention rules than biometric data such as heart rate or brain signals.
- Note that some health-related information may qualify as medical data under the ADA and needs extra confidentiality.
- Minimize collection to what is necessary for safety and productivity to reduce privacy impact.
- Define the data lifecycle: collection, transfer, processing, storage, and deletion so everyone knows expectations.
Where Wearables Are Used: Practical Employer Use Cases Across Industries
Different settings apply devices and sensors to meet clear goals. In heavy industry, employers use wearables for fatigue monitoring, posture correction, and proximity alerts to cut injuries and incidents.
In healthcare, devices support safe lifting, patient handling, and infection-control monitoring. These use cases rely on timely data and strict confidentiality.
Corporate settings lean toward wellness programs and limited productivity insights. Retail and service employers track time, location, and queue activity to improve the customer experience.
Logistics and field work use GPS-enabled devices for routing, lone-worker alerts, and fast incident response. Across these settings, you must design data flows so managers only see what they need for safety and operations.
- High-risk sites: construction and manufacturing monitor fatigue, posture, and hazard proximity.
- Clinical spaces: focus on safe handling and infection metrics.
- Customer-facing: timekeeping, location, and queue management guide staffing.
Be mindful of employee concerns. Tailor transparency, set access rights by function, and establish clear guardrails for when activity and location collection is allowed.
EEOC’s 2024 Fact Sheet and the Legal Landscape You Must Navigate
You should view the EEOC’s 2024 fact sheet as a road map for lawful collection and careful use of employee data. Follow it to reduce legal exposure and to design practical controls.
Collecting information, using information, and accommodations: the EEOC’s three risk areas
The fact sheet groups risk into three areas: collection, use, and reasonable accommodations. Limit collection to what is job-related and consistent with business necessity.
ADA, Title VII, and GINA: core federal nondiscrimination anchors
Health-related collection can trigger ADA rules and may count as a medical exam. You must avoid adverse actions based on biased or inaccurate outputs under Title VII or GINA.
NLRB concerns about surveillance and Section 7 rights
The NLRB warns that monitoring may chill concerted activity. Design access controls so supervisors see only the information they need.
AI-related equity, inclusion, and accessibility risks highlighted by federal agencies
Validate vendor claims and test for bias, especially where sensors show less accuracy across different skin tones. Document mitigation steps and track state laws on biometric data and notices.
“Treat federal guidance as a compliance checklist—collect less, justify more, and keep safeguards visible.”
- Action: Map collection, use, retention, and access.
- Action: Require consistent business necessity before any medical inquiry.
- Action: Test AI and prohibit decisions that rely on biased outputs.
Data Collection Rules: Job-Related and Consistent with Business Necessity
Set clear rules so health signals are only gathered when they directly support a defined job task. The EEOC warns that readings such as blood pressure or vital signs can become a medical examination or a disability-related inquiry under the ADA. You must avoid mandatory collection unless it meets a documented test of job relevance.
When health data may trigger ADA protections
Collecting biometric health metrics can create legal exposure if it is not tied to a specific safety or performance need. Make the decision in writing and link the measure to a work-related risk or duty.
Defining and documenting business necessity
Describe the business necessity and save that rationale before any collection begins. Use intake checklists to evaluate proportionality and keep a review cadence so necessity is revalidated when risks or technology change.
Segregating medical information and limiting access
Store ADA-covered records separately from personnel files and restrict access. Let supervisors see only the minimum information needed for operations. Record retention timelines and decisions so you can show compliance in audits.
- Distinguish safety-critical metrics from wellness data.
- Apply access controls by role to protect employee privacy.
- Cover both employer-issued and employee-owned devices when work information is shared.
Consent, Transparency, and Employee Rights
Make transparency your default: clear notices reduce confusion and build confidence among staff. You should open with a readable summary that explains what data you collect, why you collect it, who can access it, and how long you retain it.
Voluntary vs. mandatory participation
Be explicit: tell employees which programs are voluntary and which uses are required for safety. Voluntary offerings must not be presented in a way that coerces participation.
What informed consent must cover
Design consent forms in plain language. Cover data scope, intended use, permitted access, retention periods, and the right to withdraw consent at any time.
- Short notices: give a one-paragraph summary plus a link to full details.
- Revocation: explain how an employee can revoke consent and what that means operationally.
- Documentation: log approvals, changes, and withdrawals so you can show compliance.
Wellness programs and EEOC rules
If you offer wellness incentives or devices, review EEOC guidance closely. Consent never replaces legal limits under ADA, GINA, or Title VII.
Declining and requesting accommodations
Make it clear that employees can decline participation, request reasonable accommodations, and raise concerns without retaliation. Train managers to respect those choices and to route accommodation requests properly.
“Consent must be informed, voluntary, and revocable; it should never be a shortcut around legal protections.”
For an example of training on employee-facing technology and data use, see VR employee training resources.
Preventing Bias, Inaccuracy, and Discrimination in Wearable Technologies
Start by testing devices and models in real work conditions so you can spot gaps before decisions rely on outputs. Pilot data collection across diverse roles and body types to confirm vendor claims. This helps you avoid surprises when information informs management choices.
Accuracy gaps for different skin tones and body types
Devices may read differently across skin and body variations. The EEOC flagged risks where sensors underperform on darker skin tones, producing skewed results. You should require vendors to prove accuracy across groups and verify performance during pilots.
Avoiding adverse actions tied to protected characteristics
Do not base discipline or hiring choices on unverified outputs. Create clear rules that forbid adverse employment decisions using noisy metrics. Document Title VII safeguards and require human review before any action that affects assignments, evaluations, or schedules.
- You will require vendor validation across skin tones and body types during pilots.
- You will ban adverse decisions based on biased or low-confidence data.
- You will set escalation paths so employees can challenge conclusions and request human review.
- You will validate artificial intelligence features with bias testing, drift monitoring, and remediation steps.
- You will limit sensitive signals to operational insight unless independently corroborated and meet quality thresholds.
“Validate accuracy first and keep privacy front and center when investigating anomalies.”
Keep documentation of tests, thresholds, and remediation actions so regulators and employees can see how you reduce discrimination risks. This protects employees and employers while making data-driven activity fairer and more reliable.
Privacy, Security, Retention, and Data Minimization
Treat data handling as an operational requirement: control access, limit retention, and test vendor safeguards. Build rules that keep medical records separate and reduce the risk that sensitive information shapes employment outcomes.
Confidential handling of ADA-covered information
Store medical and disability records in separate, confidential files. Keep them out of personnel folders and restrict access to designated medical reviewers.
Log every access so you can show why someone viewed a record and when.
Security safeguards for biometric data and breach obligations
Encrypt biometric data at rest and in transit and adopt strong key management. Align your breach response with state notification rules and document each step and timeline.
Require vendors to support encryption, audits, and rapid notification where laws demand it.
Retention limits, purpose limitation, and minimization
Map all data collection points and keep only what you need. Define retention schedules by data type and enforce automated purges for high-sensitivity records.
Managing third-party sharing with insurers and vendors
Vet vendors, require contractual security controls, and limit downstream use to documented, employee-protective purposes. Review manufacturer updates for firmware or cloud changes that alter data flows.
- Access controls: strict separation of medical files from HR records.
- Minimization: collect only necessary signals and set short retention windows.
- Vendor rules: contracts for security, subprocessors, audits, and breach notice.
“Purpose limitation and documented retention turn raw monitoring into accountable practice.”
State Laws, Location Tracking, and International Considerations
Before you expand deployments, confirm which state and global laws limit tracking, biometric uses, and electronic monitoring. Map where you operate and note state rules on biometric data, location tracking, and written notice requirements. This upfront step avoids costly fixes later.
Biometric regimes and consent for location tracking
Illinois and Texas regulate biometric data, and Colorado requires consent before you collect biometric information. Hawaii and New Jersey added notice or consent rules for workforce location tracking. Nearly 20 states now have statutes that affect how you capture location data.
Written notices and microchip prohibitions
New York, Connecticut, and Delaware require written electronic monitoring notices. Several states also ban mandatory microchip implants. Make these bans explicit in your program and document how you meet written notice rules.
International rules and cross-border implications
Most countries require notice, individual rights, retention limits, and strict transfer controls. If you move information across borders, use approved transfer mechanisms and engage local counsel to confirm retention and security obligations.
- Inventory jurisdictions and map applicable laws.
- Design consent and notice flows for location features.
- Limit monitoring to safety or operational necessity and time-bound collection.
- Document compliance for audits and provide a simple channel for employee rights and concerns.
“Inventory first, notify clearly, and restrict access to what is necessary.”
Building Your Wearable Tech Policy: A Best Practices Guide
Begin with a short scope statement that lists covered devices, the data collected, and authorized uses. That simple opening sets expectations for managers and employees and prevents function creep.
Define scope: devices, data collected, and authorized uses
List covered devices and the types of data you will collect. Name permitted uses and clearly flag prohibited uses so you avoid surprise monitoring.
Set rules for collection, use, monitoring, and necessity thresholds
You will require written justification before adding new collection or monitoring. Document business necessity and review it regularly.
Detail privacy, security, retention, and access controls
Segregate ADA-covered records and limit access by role. Define retention windows and enforce encryption, audits, and owner accountability.
Document accommodation, complaint, and escalation procedures
Include clear steps for accommodation requests, complaints, and rapid escalation. Train managers, HR, and IT to follow consistent practices.
- Standardize vendor contracts and procurement to protect data and require update notices.
- Require quality and bias testing; define remediation if activity metrics are unreliable.
- Align wellness programs with EEOC rules and forbid cross-use of operational data in performance reviews.
“Documented rules, clear roles, and routine testing turn technology into a safer, fairer resource.”
Operationalizing Compliance: Governance, Training, and Vendor Management
Put governance structures in place so operational choices follow clear legal and ethical lines. Assign clear owners for legal, HR, IT/security, and business functions so someone is accountable every day.
Assigning roles and daily oversight
You should name responsible leads who approve deployments, review contracts, and sign off on retention and access rules.
Legal handles regulatory interpretation. HR manages employee-facing issues. IT/security enforces controls. Business owners justify use cases.
Training managers to avoid misuse and discrimination
Train supervisors to treat metrics as one input, not the sole basis for decisions. Teach escalation and accommodation steps so employees can raise concerns safely.
Vetting vendors and testing for bias
Vet providers for security, privacy, and accuracy. Require contractual rights to audits, updates, and breach notice. Test models for bias and monitor artificial intelligence features or firmware changes that affect data flows.
- Roles: assigned owners across teams for daily actions and audits.
- Training: prevent discrimination and overreliance on metrics.
- Vendors: contracts that protect employee data and require tests.
- Audits: periodic reviews, bias testing, and change management gates.
“Build governance that adapts as laws, standards, and manufacturer updates change.”
Measure success with simple KPIs: fewer complaints, faster approvals, and reduced incidents. Track legal updates so employers must adjust practices and keep employees protected.
Conclusion
Conclusion
You now have a clear blueprint to unlock value from wearables while protecting privacy and meeting legal expectations. Focus on narrow data collection, transparent use, and vendor validation so you limit risk and improve trust.
Commit to fairness: test for bias, prevent discrimination, require human review for major decisions, and document accommodations and opt-outs. Operationalize governance, training, and vendor controls so your program adapts as laws change.
Measure outcomes, retain only needed activity data, and iterate. For practical steps and workplace examples, see the smart workplace guide. Do this and your employers and employees will better protect rights and seize the employment opportunity these settings offer.